Bridging the IT/OT Gap: A Field Architect’s Guide to IoT Edge Gateways and Protocol Translation
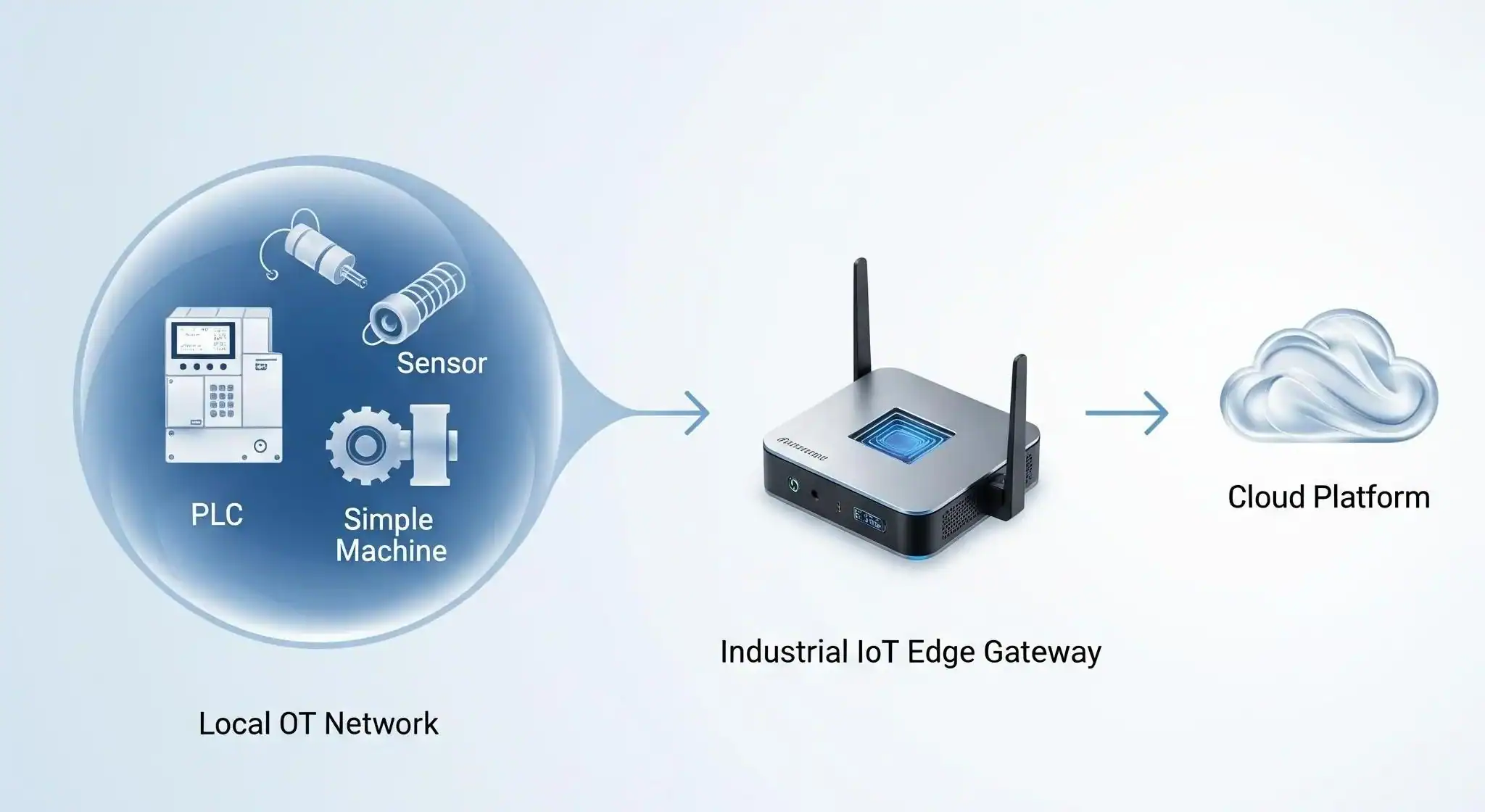
In mission-critical Industrial IoT, direct cloud connectivity for every sensor is often impossible due to legacy protocols, security mandates, or network constraints. This creates a “data island” effect that stalls digital transformation. This technical guide provides a roadmap for using an Industrial IoT Edge Device as a Gateway to solve these connectivity gaps.
What You Will Learn:
- Architecture Selection: Deciphering the Transparent Gateway vs. Protocol Translation patterns for your specific OT environment.
- Legacy Integration: How to bridge Modbus RTU/TCP and serial assets into a modern MQTT/JSON cloud stream.
- Edge Orchestration: Leveraging the Robustel EG5120‘s NXP i.MX 8 power and Docker-based environment for real-time data normalization.
- Security Hardening: Implementing IEC 62443 standards and WireGuard VPNs to create a “Zero-Trust” frontier at the edge.
Introduction: Bridging the IT/OT Connectivity Gap
I’ve spent a lot of time on factory floors and at remote utility sites, and the “Last Mile” connectivity challenge is always the same: you have a wealth of valuable data trapped in legacy equipment. Whether it’s sensors speaking Modbus RTU, actuators on a serial bus, or newer Bluetooth Low Energy (BLE) devices, they all share one problem—they weren’t built for the modern internet.
These assets are effectively “data islands”. So, how do you bridge the gap between rugged field hardware and your cloud analytics platform?
The solution isn’t just a simple modem; it’s an intelligent intermediary. By deploying a dedicated Industrial IoT Edge Gateway, you aren’t just “connecting” devices—you are creating a secure, high-compute front door for your entire operation. This guide breaks down the architecture of using an IoT Edge Device as a Gateway, moving beyond basic connectivity to real-time, localized data orchestration.
Deciphering Gateway Patterns—Architecture for the Edge
Not all edge deployments are created equal. When configuring an Industrial IoT Edge Gateway, your choice of architecture depends entirely on your field assets. While industry giants like Microsoft Azure IoT Edge have standardized these models, they generally boil down to two high-impact patterns.
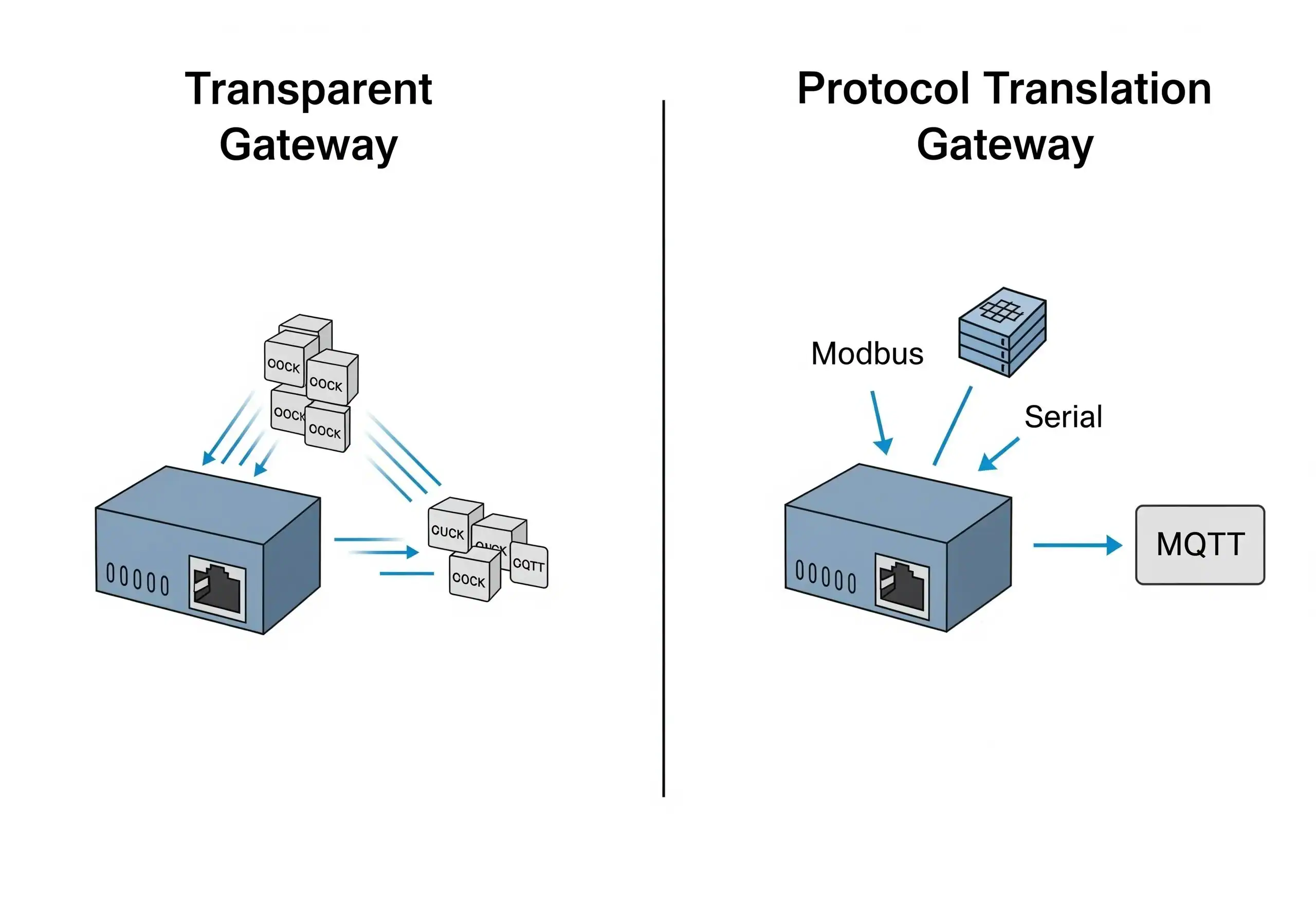
Pattern 1: The Transparent Gateway (The Secure Pipe)
Think of this as a “pass-through” architecture.
- How it works: In a transparent setup, the edge device acts as a secure intermediary. Downstream devices maintain their own unique identities in the cloud but communicate through the gateway.
- The Technical Role: The gateway handles the TLS encryption and cloud authentication, but it doesn’t “open the envelope” of the data. It simply ensures a secure, reliable pipe to the IoT Hub.
- Best for: Modern devices that already speak MQTT or HTTPS but are restricted by local firewalls or lack direct internet access.
Pattern 2: The Protocol Translation Gateway (The Intelligent Translator)
This is where the true power of an IoT Edge Device is unlocked for industrial environments.
- How it works: Here, the gateway acts as a bilingual master. It speaks the “Southbound” language of your shop floor (Modbus RTU/TCP, OPC UA, or BACnet) and translates that raw telemetry into a standardized “Northbound” format like JSON over MQTT for the cloud.
- The Technical Role: Downstream devices (like PLCs or VFDs) remain completely isolated from the internet. The gateway takes full responsibility for protocol conversion, data normalization, and buffering during network outages.
- Best for: Industry 4.0 initiatives that require connecting legacy OT (Operational Technology) to modern IT systems. If you have serial-based sensors or decades-old PLCs, this is your non-negotiable solution.
Field Implementation—The Robustel EG5120 in Action
To move from theory to deployment, you need a hardware platform that balances rugged reliability with open-source flexibility. The Robustel EG5120 is a benchmark for an Industrial IoT Edge Gateway designed specifically for high-performance protocol translation.
Why the EG5120 is Built for the Edge
- High-Compute NXP i.MX 8 Processor: Its quad-core architecture provides the deterministic horsepower required to manage complex concurrent protocol translations and local analytics without latency.
- Integrated Industrial I/O: Built-in RS232/RS485 serial ports and isolated DI/DO mean you can interface directly with legacy PLCs or sensors, eliminating the need for fragile external adapters.
- RobustOS Pro (Debian-based): By providing a native Linux environment with Docker support, the EG5120 allows you to deploy containerized microservices—like custom Python scripts or Node-RED flows—in minutes.
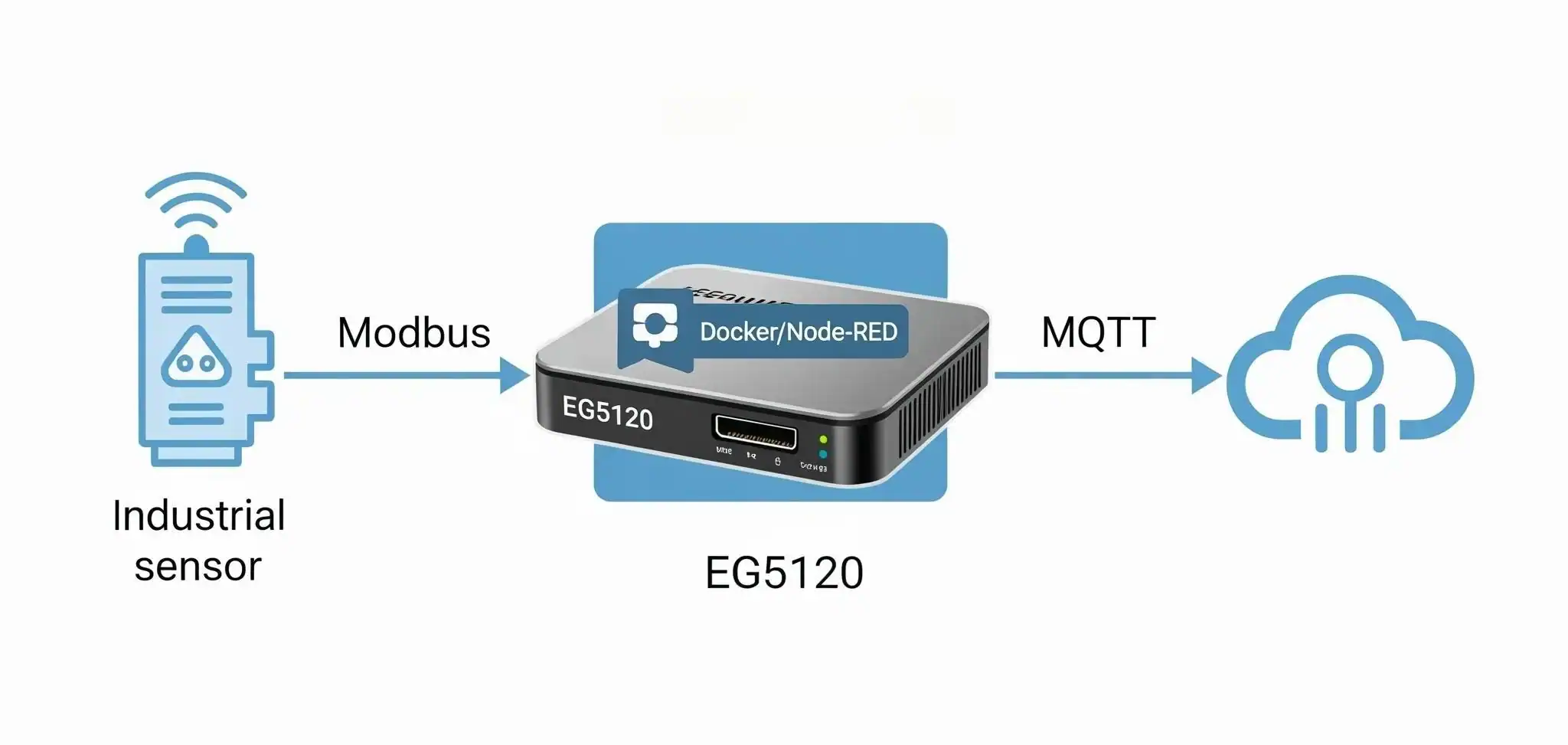
A Real-World Scenario: Bridging Modbus RTU to MQTT
Here is how the “translation” looks in a live industrial environment:
- Physical Interfacing: A legacy Modbus RTU temperature sensor is wired directly to the EG5120’s RS485 terminal.
- Edge Processing & Normalization: A Node-RED container on the gateway polls the Modbus register every 10 seconds. It doesn’t just pass the raw data; it scales the integer into a Celsius float and packages it into a structured JSON payload: {“device_id”: “sensor_01”, “temp_c”: 25.5}.
- Secure Uplink: The gateway leverages its integrated 4G/5G cellular backhaul to publish this normalized data to a cloud-based MQTT broker (such as Azure IoT Hub or AWS IoT Core).
Through this localized intelligence, a decades-old serial sensor is instantly transformed into a high-fidelity Industry 4.0 asset, with the IoT Edge Device serving as the critical translation layer.
Mission-Critical Security—Fortifying the Edge Gateway
When a single IoT Edge Device serves as the central conduit for an entire fleet of sensors and PLCs, its security posture determines the resilience of your entire OT network. A compromised gateway is a single point of failure; therefore, a multi-layered defense strategy is non-negotiable.
1. Hardening the Gateway Host
Security starts at the silicon level. For an Industrial IoT Edge Gateway, ensure the OS environment is fully hardened:
- Immutable Trust: Look for a Secure Boot process that prevents unauthorized firmware from executing.
- Development Standards: Prioritize vendors whose product lifecycle is certified to IEC 62443-4-1, ensuring security is “baked in” from the design phase.
- Granular Control: A robust local firewall (like nftables) is essential to minimize the attack surface.
2. Segmenting Downstream Assets
Never treat your local sensor network as a “trusted zone”.
- Network Isolation: Downstream devices should be isolated on dedicated VLANs or physical subnets, communicating with the gateway only via strictly defined protocols. This prevents lateral movement in the event of a breach.
3. Securing the Cloud Uplink
The “Northbound” connection to your cloud broker must be an encrypted fortress:
- Encryption & Tunnels: Always use TLS 1.3 for MQTT traffic and encapsulate sensitive telemetry within high-performance VPNs like WireGuard or OpenVPN.
- Certificate Management: Implement X.509 certificate-based authentication instead of static passwords to ensure only verified gateways can talk to your IoT Hub.
Conclusion: Scaling the Future of Industrial Connectivity
Configuring an IoT Edge Device as a Gateway is no longer just an architectural choice—it’s a strategic necessity for the modern industrial landscape. Whether you are implementing a Transparent Gateway to navigate restrictive enterprise firewalls or deploying a Protocol Translation Gateway to breathe new life into legacy serial assets, the success of your deployment hinges on three pillars: Processing Power, Software Extensibility, and Industrial-Grade Reliability.
The Robustel EG5120 was engineered to bridge these exact gaps. By combining an open Debian-based environment with the deterministic performance required for real-time edge analytics, it provides a production-ready foundation for your Industry 4.0 roadmap.
As you move from proof-of-concept to global scale, remember that the “Gateway” is more than a bridge—it is the intelligent frontier where your raw operational data transforms into actionable business intelligence.
FAQs
Q1: What’s the main difference between using an IoT Edge device as a gateway and a simple router?
A1: A simple router just forwards IP traffic. An IoT Edge device as a gateway is an intelligent computer. It can understand and translate non-IP protocols (like Modbus), run custom applications locally (edge computing), and manage the identities and security for downstream devices.
Q2: Do all IoT Edge devices support these gateway patterns?
A2: Not all. The ability to function effectively as a protocol translation gateway depends on the device having the right physical interfaces (like serial ports), a flexible OS (like Debian-based RobustOS Pro), and support for running custom software (like Docker containers).
Q3: How many downstream devices can connect to one IoT Edge Gateway?
A3: This depends on the gateway’s processing power and the amount of traffic each device generates. For simple protocol translation with low data rates, a powerful device like the EG5120 could handle dozens or even hundreds of downstream devices.
About the Author
Robert Liao | Technical Support Engineer
Robert Liao is an IoT Technical Support Engineer at Robustel, specializing in industrial networking and edge connectivity. A certified Networking Engineer, Robert focuses on the deployment and troubleshooting of large-scale IIoT infrastructures. His work centers on architecting reliable, scalable system performance for complex industrial applications, bridging the gap between field hardware and cloud-side data management.
