Edge Router vs. Firewall: Building a Lean, Secure Industrial Network Perimeter
The edge router vs. firewall debate is often a misunderstanding of roles. In modern Industrial IoT (IIoT), the boundary has vanished: a firewall is a security function that an industrial edge router must integrate by design. This guide simplifies your network architecture by deconstructing why a single, hardened device is often superior to redundant IT hardware.
- The Convergence: Why a professional edge router is, by definition, a stateful firewall (Layer 3/4), providing the primary defense layer for the network perimeter.
- OT vs. IT Security: Why specialized Next-Generation Firewalls (NGFW) are often an expensive “IT tax” for industrial sites that prioritize low latency and invisible perimeters over application-level filtering.
- Strategic Verdict: For 90% of industrial deployments, an edge router with integrated VPN and stateful inspection offers the best balance of TCO (Total Cost of Ownership) and mission-critical reliability.
Introduction: The Converged Edge—Is the Firewall/Router Divide Dead?
If you are architecting a secure network for a smart factory or a remote site, you have likely encountered a recurring dilemma: “Do I need a dedicated firewall, or does an industrial edge router provide sufficient protection?”
In my experience, significant budgets are often misallocated—either through redundant hardware or insufficient security—due to this fundamental confusion. Let’s clarify: A firewall is a security function; an edge router is a mission-critical device. By 2026, any professional industrial edge router must act as a sophisticated firewall to survive the modern threat landscape.
The boundary between routing and security has effectively blurred, creating a converged edge. This evolution is a major advantage for Industrial IoT (IIoT) deployments, as it allows a single, hardened device to serve as your secure border checkpoint. To understand how to protect your data without over-complicating your rack, let’s break down the evolving roles of the edge router vs. firewall.
What is a Firewall? (The Intelligent Border Guard)
At its core, a firewall acts as the specialized security guard for your industrial network. Its primary directive is to stand at the network perimeter and scrutinize every data packet attempting to enter or exit. By comparing these packets against a strict Access Control List (ACL), it makes an instantaneous decision: Allow or Deny.
However, in a mission-critical IIoT environment, the “intelligence” of that guard is what defines your risk profile.
1. The “Dumb” Firewall (Basic Packet Filtering)
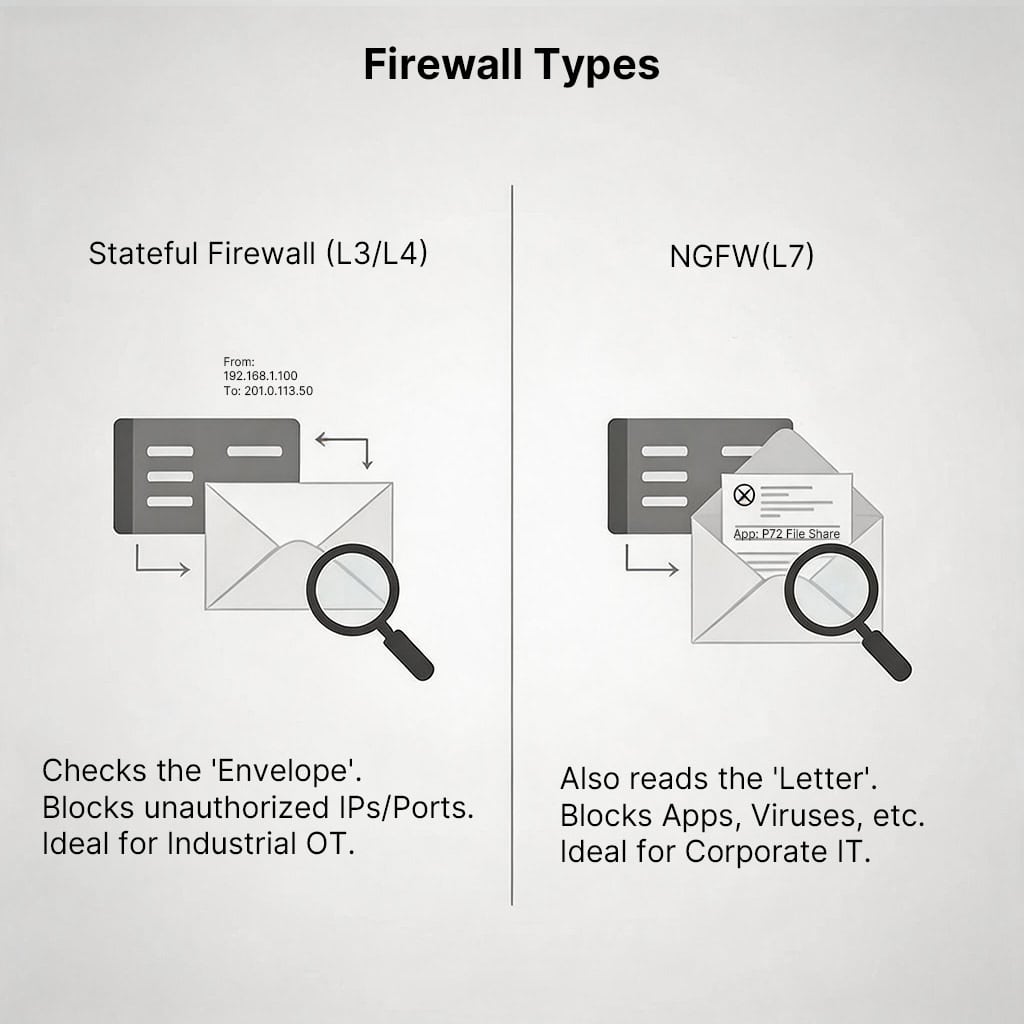
Traditional packet filtering operates only at the surface level (Layer 3 and Layer 4 headers). It simply looks at the “envelope” of the data—source IP, destination IP, and port.
- The Constraint: It lacks context. If a rule says “Allow IP 1.2.3.4,” the firewall will let it through regardless of whether that packet is a requested update or a malicious intrusion. In a modern factory, this “stateless” approach is no longer sufficient.
2. The “Smart” Firewall (Stateful Inspection)
This is the modern industry standard and the baseline for any reliable industrial edge router. A stateful firewall is essentially a guard with a memory.
- How it Works: When your PLC (Programmable Logic Controller) or edge device sends a request to a remote server, the firewall records this in its state table. When the response returns, the firewall confirms it is part of an established, legitimate conversation before granting access.
- Enhanced Security: If a cyber-threat attempts to send an unsolicited packet—even from a known server—the firewall finds no matching entry in its state table and immediately denies the connection.
The Bottom Line: Stateful Packet Inspection (SPI) is the foundation of modern industrial network security. It ensures that your edge router isn’t just forwarding traffic, but actively preventing unauthorized “uninvited guests” from penetrating your local network.
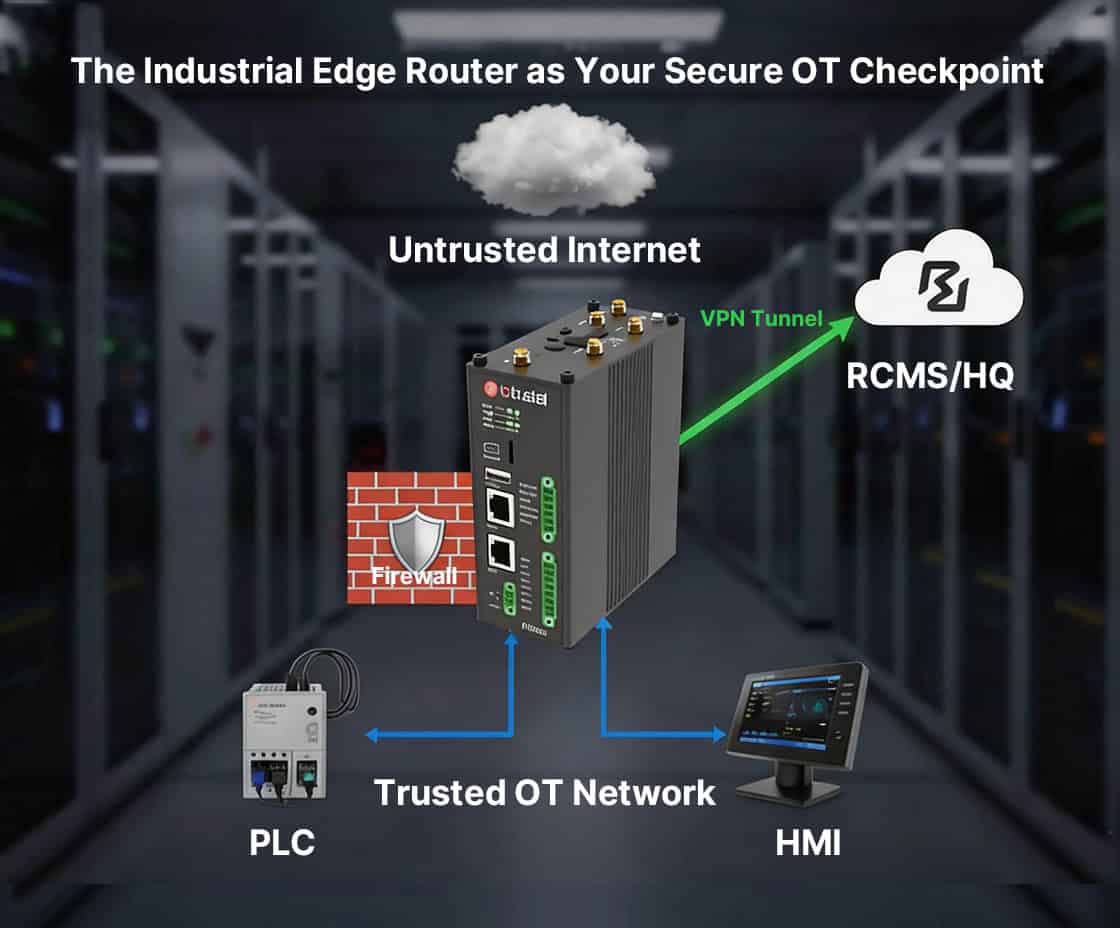
The Industrial Edge Router—A Unified Border Checkpoint
Building on the security foundations we’ve discussed, the industrial edge router serves as the physical “border checkpoint” for your operations. Its primary mandate is to manage the critical interface between your trusted Internal LAN (Local Area Network) and the untrusted External WAN (Wide Area Network/Internet).
Because the edge router sits at the very edge of your network architecture, it is the first—and often the most vital—line of defense.
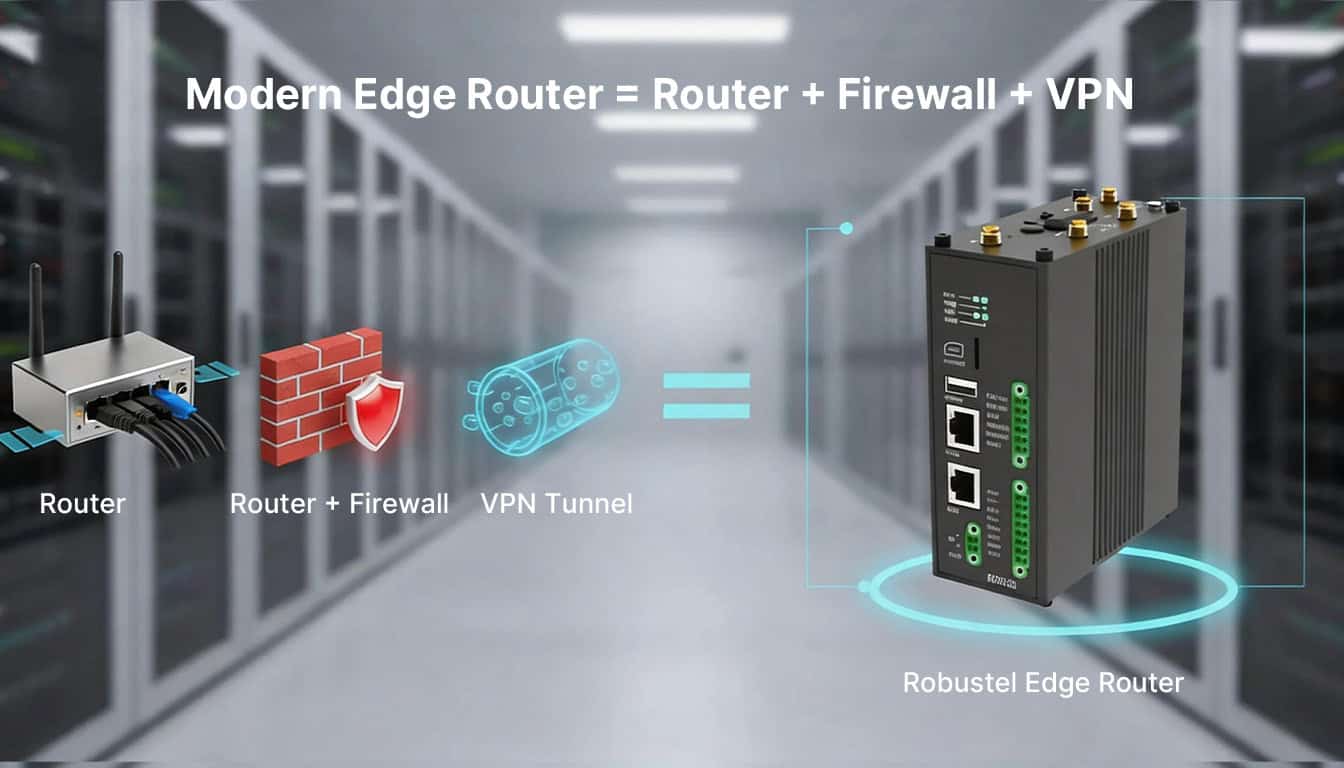
In the legacy networking era of the 1990s, organizations typically deployed a standalone router and a separate firewall appliance. In today’s Industrial IoT (IIoT) landscape, these capabilities have converged into a single, hardened device. A modern industrial edge router is a multi-functional platform designed to handle three core pillars:
- Intelligent Routing: Orchestrating North-South traffic between the factory floor and the cloud with high precision.
- Integrated Firewalling: Operating as a built-in stateful firewall to neutralize external threats before they reach your local infrastructure.
- Encrypted Connectivity: Functioning as a secure VPN endpoint (IPsec, OpenVPN) to ensure all data traversing the WAN remains fully encrypted.
The Strategic Shift: For modern deployments, you no longer need to manage two separate hardware ecosystems. You simply deploy an edge router that integrates a powerful, industrial-grade firewall by design.
The Integrated Edge—Why Your Router is Your Best Firewall
For the vast majority (99%) of industrial, retail, and remote branch deployments, the most efficient architecture is one where your edge router functions as your primary security appliance. Consolidating these roles into a single, hardened device minimizes latency, reduces the attack surface, and significantly lowers the total cost of ownership (TCO).
When you deploy a Robustel industrial edge router—such as the high-speed R5020 Lite (5G Edge Router) or the powerful EG5120 (Edge Computing Gateway)—you are installing more than a connectivity tool; you are deploying a robust security engine. Powered by RobustOS, our devices transform into a comprehensive security stack:
- Enterprise-Grade Stateful Firewall: RobustOS includes a sophisticated stateful engine that monitors the “health” of every connection, ensuring only verified traffic penetrates your perimeter.
- High-Performance VPN Hub: Functioning as a high-throughput VPN endpoint, it enables the rapid creation of encrypted IPsec, WireGuard, or OpenVPN tunnels to protect your data in transit.
- OT/IT Network Segmentation: This is critical for Industrial Cyber-Physical Security. You can configure firewall rules to create a “DMZ” (Demilitarized Zone), effectively isolating mission-critical OT assets—like PLCs and sensors—from the broader IT office network.
By leveraging a single, industrial-grade edge router for both routing and security, you eliminate the complexity of managing multiple hardware vendors while maintaining a “Defense-in-Depth” posture at the network edge.
The NGFW Distinction—Industrial Precision vs. Corporate Overkill
This leads us to the final piece of the puzzle: The Next-Generation Firewall (NGFW). In the enterprise IT world, vendors like Fortinet or Palo Alto emphasize NGFW capabilities, leaving many to wonder if an industrial edge router is truly enough.
The reality is quite simple: An NGFW is essentially a hyper-specialized edge router that adds a processor-intensive layer known as Deep Packet Inspection (DPI).
Layer 7 Inspection: Reading the Mail
While a standard stateful firewall looks at the “envelope” (IPs and Ports), an NGFW “opens the mail.” It operates at Layer 7, identifying specific applications and signatures within the data stream.
- The IT Use Case: Identifying if an employee is accessing a restricted file-sharing app or detecting a specific ransomware signature hidden in a web download.
- The OT Reality: On the factory floor, your PLC or Remote Terminal Unit (RTU) isn’t browsing social media or downloading unverified files. In most Industrial IoT scenarios, Layer 7 inspection is an expensive “overkill” that adds unnecessary latency and complexity.
Why “Invisible” is Better than “Inspected”
For 90% of OT security requirements, your goal isn’t to manage user behavior, but to make your industrial network invisible to the outside world. An industrial edge router like those from Robustel is designed to execute this high-security mission perfectly through three fundamental rules:
- Implicit Deny: Block all unsolicited incoming traffic by default.
- Controlled Access: Only permit authenticated VPN tunnels from your central Command Center.
- Strict Outbound Filtering: Only allow MQTT or Modbus-TCP data to travel to a pre-verified cloud IP address.
The Conclusion for Decision Makers: You don’t need a $5,000 corporate NGFW to secure a remote pump station or an automated assembly line. A high-performance Robustel EG series provides the exact Layer 3/4 stateful security needed to harden your industrial perimeter without the “IT tax.”
Conclusion: Simplified Security—Choosing the Right Tool for the Edge
To resolve the edge router vs. firewall debate, we must shift our perspective: stop viewing them as competing hardware and start seeing them as a unified solution. A firewall is not an extra box; it is a fundamental security feature that your industrial edge router must possess by design.
The decision-making framework is straightforward: you don’t need “one of each”—you need a single device equipped with the specific security intelligence your application demands.
- For Corporate IT (Protecting Human Behavior): If your goal is to inspect web browsing and manage employee applications, a Layer 7 NGFW is the appropriate, albeit complex, tool.
- For Industrial OT (Protecting Machine Assets): If your goal is to harden a remote site or factory floor, you need a rugged industrial edge router (like a Robustel) that excels at Layer 3/4 Stateful Firewalling and high-throughput VPN tunneling.
Ultimately, a professional-grade industrial edge router is your complete security solution. When combined with a centralized management platform like RCMS (Robustel Cloud Manager Service), you can orchestrate firewall rules and VPN certificates across your entire edge router fleet from a single pane of glass. This ensures that your security posture is not only robust but consistently updated against emerging threats.
よくある質問
Q1: Is an edge router secure enough, or do I still need a separate, dedicated firewall?
A1: For 99% of branch office, retail, and industrial applications, a professional edge routeris your firewall. It is designed for this job. A separate firewall is redundant unless you have highly specialized needs, like requiring the Layer 7 (application-level) inspection of a Next-Generation Firewall (NGFW).
Q2: Does an edge router do NAT (Network Address Translation)?
A2: Yes. NAT is a core function of any edge router. NAT is the technology that translates your 100 private, internal LAN IP addresses (e.g., 192.168.1.x) into the one, single, public IP address provided by your internet provider.
Q3: Is the Robustel R5020 Lite (a 5G router) a true edge router and firewall?
A3: Absolutely. The R5020 Lite is a perfect example of a modern industrial edge router. It provides 5G/4G WAN connectivity, and its RobustOS includes a powerful stateful firewall and a full suite of VPN clients (IPsec, OpenVPN, WireGuard) to secure your network perimeter.
著者について
Robert Liao | Technical Support Engineer
Robert is an IoT Technical Support Engineer at Robustel, specializing in industrial networking and edge connectivity. A certified Networking Engineer, Robert focuses on the deployment and troubleshooting of large-scale IIoT infrastructures. His work centers on architecting reliable, scalable system performance for complex industrial applications, bridging the gap between field hardware and cloud-side data management.
